QIT Solutions: Blog
The Hidden Data Risks of AI Chatbots: What Businesses Need to Know
Artificial intelligence chatbots like ChatGPT, Microsoft Copilot, and Google Gemini are now common in the workplace. Teams use them to summarize meetings, draft proposals, analyze data, or even brainstorm strategies. The productivity gains are real, but so are the risks.…
Read More about The Hidden Data Risks of AI Chatbots: What Businesses Need to KnowConsent Phishing: What Every Business Needs to Know
As an MSP, we see cyber threats evolve faster than many businesses can adapt. One of the quieter but increasingly dangerous attack methods is Consent Phishing. Unlike traditional phishing emails that trick users into giving up passwords, consent phishing tricks…
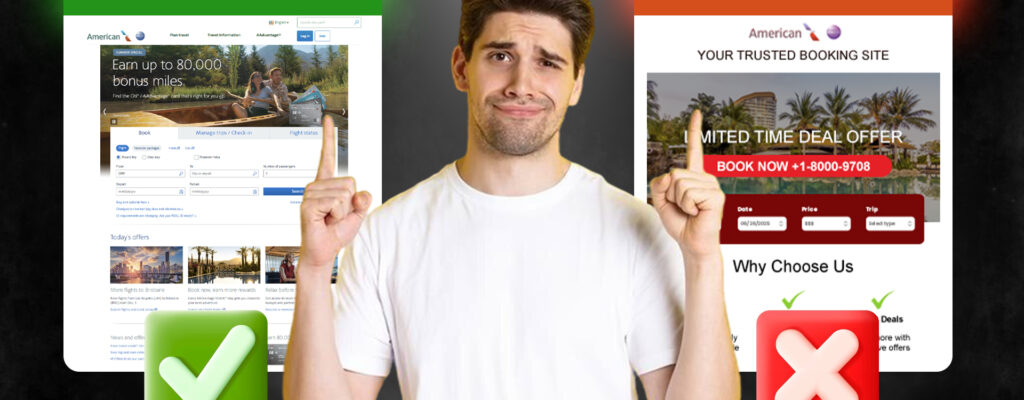
Read More about Consent Phishing: What Every Business Needs to KnowThe One Click That Could Ruin Your Vacation
Just because summer is winding down doesn’t mean the travel risks are. Whether you’re squeezing in one last vacation or planning a Labor Day escape, it’s good to stay alert. Cybercriminals are always looking for ways to exploit unsuspecting travelers,…
Read More about The One Click That Could Ruin Your VacationBeach‑Side Browsing: 7 Quick Ways to Lock Down Public Wi‑Fi Before You Hit ‘Connect’
As we head out on summer vacations, the need for internet access grows. However, using public Wi‑Fi networks can pose significant risks to our data. We need to secure our connection to protect sensitive information. Using unsecured public wi‑fi can…
Read More about Beach‑Side Browsing: 7 Quick Ways to Lock Down Public Wi‑Fi Before You Hit ‘Connect’How AI Is Supercharging Cyber Threats This Summer
Long days and warm nights make summer the perfect time to unplug and unwind. But while you’re kicking back, cybercriminals are ramping up. And this year, they’ve got a powerful sidekick: artificial intelligence. AI is making scams faster, smarter, and…
Read More about How AI Is Supercharging Cyber Threats This SummerSummer Cybersecurity: Keeping Kids Safe Online During Break
When the final school bell rings for summer, kids often swap homework for screens. With more free hours in the day, activities like gaming, streaming, and social media quickly take center stage. Yet, with that freedom comes risk. From online…
Read More about Summer Cybersecurity: Keeping Kids Safe Online During BreakNavigating the New HIPAA Security Rule NPRM: What Healthcare Providers Need to Know
The healthcare industry is undergoing major regulatory changes that will impact cybersecurity and compliance standards. The proposed updates to the HIPAA Security Rule, known as the Notice of Proposed Rulemaking (NPRM), introduce stricter requirements for protecting electronic protected health information…
Read More about Navigating the New HIPAA Security Rule NPRM: What Healthcare Providers Need to KnowGraduation Season: Protecting Young Adults from Cyber Threats
The diploma isn’t even framed yet, and hackers are already rolling out the welcome mat. The moment graduates start job hunting, their personal data becomes prime real estate for cybercriminals. Fake recruiters, phishing emails posing as HR, and password-stealing scams…
Read More about Graduation Season: Protecting Young Adults from Cyber ThreatsBeyond Password Day: Are Your Passwords Still Strong Enough?
Every year, the list of most common passwords makes its way around the internet, and every year, it’s just as concerning. People are still using “123456” and “password” like it’s 1999. Meanwhile, cybercriminals don’t need cutting-edge hacking tools when people…
Read More about Beyond Password Day: Are Your Passwords Still Strong Enough?Protecting Your Personal Devices: Cybersecurity Tips for Home and Beyond
Your phone is more than a phone. It is a wallet, a filing cabinet, a work desk, and a personal vault — and hackers know it. The same goes for laptops and tablets, which store everything from financial records to…
Read More about Protecting Your Personal Devices: Cybersecurity Tips for Home and BeyondHow can we help?
Whether you need immediate help with an IT issue or want to discuss your long-term IT strategy, our team is here to help.
Call us at +1 844-855-4748 or complete the form below and we'll help in any way we can.